This article is more than 1 year old
Was Bush packing Wi-Fi in TV debate?
Miraculous clarity arouses suspicion
Opinion Wireless technology might explain why US President George W. Bush performed better than usual in the last two presidential debates with his opponent, Senator John Kerry.
Unless he's reading a well-rehearsed speech, the President is normally much given to malapropisms and incoherent syntax. When confronted with questions for which he is not prepared, he typically muddles along unintelligibly when starting a reply, until he finds a path to one of his prepared talking points, as he repeatedly did during his televised prime-time press conference of 13 April 2004. It is not unusual for him to take refuge in his prepared points, regardless of what question is asked, and his answers are often irrelevant as well as confused. That is, he tends to stay "on message," rather than "on topic".
Yet, during both presidential debates, he miraculously spoke in clear, organized sentences that were fairly relevant to the questions asked. He stumbled only occasionally, and then only briefly. The public has declared Kerry the winner of both debates - the first by a wide margin, and the second by a narrow one - but it is undeniable that the President far exceeded his baseline performance when confronting the unexpected. Or, said another way, he may have looked bad in comparison to Kerry, but he looked very good in comparison to himself.
Bush's bulge
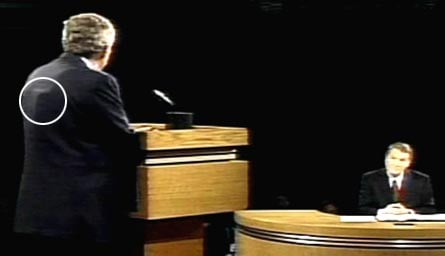
Interestingly, screen shots of the first debate, courtesy of Cryptome, show a cigarette-pack-sized object positioned between Bush's shoulders, impressing itself on his suit jacket. A wire appears to run from the object, up towards the President's neck. This is best seen in the first column, fourth picture, and in the second column, fourth picture. (Note: The Register has not verified the authenticity of these images. They appear to come from a C-SPAN feed, but we cannot vouch for that.)
The impression is consistent with common wireless gear used by public speakers and entertainers, enabling a remote coach to offer prompts and suggestions. Typically, a rig consists of a wireless radio transmitter used by the coach, and a wireless transceiver used by the speaker. For stealth, the transceiver is concealed under clothing, and connected to a flexible wire device encircling the neck and worn under the shirt, which generates a signal picked up by a wireless receiver within the ear canal, much like a small hearing aid, and virtually invisible.
Additional evidence
The pictures might be suggestive, if not conclusive, but they are not the only evidence suggesting that Bush enjoyed the benefit of a wireless hookup. The very fact that he rarely stumbled or babbled itself suggests that something extraordinary was afoot. And there were a couple of moments in both debates where Bush's behavior is best explained by presuming a remote coach.
In the first debate, during a reply to Kerry, he ranted, "Let me finish!" Oddly, neither his opponent, Senator Kerry, nor the moderator, Jim Lehrer, was attempting to cut him off, and he had plenty of time left on the clock. One explanation is that he was disoriented and confused, as he often is without a script. But a somewhat better explanation, in view of the pictures and his sudden debating competence, is that he was addressing not his opponent or the moderator, but a remote coach who had prompted him to move on to a fresh topic before he was ready to do so.
In the second debate, Bush went off the rails, again in a way that suggests remote coaching. According to the rules, each candidate answers questions in turn. The one to whom the question is addressed gets two minutes to reply, and his opponent gets ninety seconds to rebut. At the moderator's discretion, there may be a one-minute extension, providing each candidate an additional thirty seconds on each question.
At one point, when Bush had taken a question, and Kerry had delivered a spirited rebuttal, moderator Charlie Gibson decided to extend the session. But he had trouble getting the words out, as Bush leapt up and leaned into his face, repeatedly demanding the very extension that Gibson was attempting, without success, to offer him.
Kerry: "We're gonna build alliances; we're not gonna go unilaterally [into war]; we're not gonna go alone, like this President did."
Gibson: "Mr. President, let's extend for one minute..."
Bush: "Lemme just one question; I, I gotta answer this."
Gibson: "Exactly, and with reservists being held on duty..."
Bush: "Let, let me just answer this, what he said about goin' alone."
Gibson: "Well, I wanted to get into the issue."
Bush: "You tell Tony Blair we're goin' alone. Tell Tony Blair we're goin' alone. Tell Servio Belisconi we're goin' alone..."
A fair reading of the scene would have Bush's remote coach urging him to respond at that moment, with enough vehemence to distract the President from what was happening right before his eyes. "You've got to respond to that - you can't let it go. He's insulting our allies," we can imagine the coach saying. And we can imagine Bush getting flustered to the point that he failed to grasp what the moderator was trying to tell him.
Detection
Technologically speaking, it would be painfully easy for Bush to have received remote, wireless guidance during the debates. But whether he would risk pulling such a cheesy stunt is less clear. Bush may be a generous risk-taker when it comes to spilling other people's blood in Iraq, but when his own political career is at stake, he tends to play a very cautious, conservative game. If the scam were ever exposed, he would certainly lose votes that, in such a tight race, he knows he can't afford to squander. A mere pat on the back from Kerry after a debate would suffice to reveal the game.
There are other ways, too. Surveillance specialist James Atkinson has written a good generic description of the wireless device that Bush would likely have been connected to, along with a list of the radio frequencies that such devices typically employ.
All that remains is for Kerry to pat Bush down during the next debate, or for some enterprising geek to use Atkinson's information to intercept the President's coaching session, and record it. In the interest of public disclosure, we note that the final presidential debate will be held on Wednesday, 13 October on the campus of Arizona State University in Tempe, Arizona, at the Gammage Auditorium, located on the northeast corner of Mill Avenue and Apache Boulevard.
Not that we're suggesting anything. ®
Thomas C Greene is the author of Computer Security for the Home and Small Office, a comprehensive guide to system hardening, malware protection, online anonymity, encryption, and data hygiene for Windows and Linux.
Related stories
Bush gets soverized on the web
Bush's search for clean Cuban hookers goes awry
Scientists horrified by Bush's Bad Science