This article is more than 1 year old
Watching the Net's background radiation
What happens to a naked TCP/IP node?
When the city sleeps, it's never completely silent. But when the Internet sleeps, what kind of static does it make? What does it sound like? Like the weird warbles astronomers claim to hear from outer space?
We'd like to share what the Internet sounds like when it sleeps, and in its current highly agitated state, we think it's worth sharing.
Our thanks to ISP Robin Bandy at Cliq for providing traffic information for a node which died, but which was still being routed to, over several months. A silent tristero, if you like: the computer which we'll examine was giving out no TCP/IP responses. Cliq's traffic monitoring continued, however, and began to trace what the rest of us can't hear. This is the unbidden Internet traffic: the very sound of static.
What we're hearing are the pings and portscans that leave untraceable fingerprints around our sockets, and they're so slight that we don't notice. Let's look at the packets.
A daily sample shows that this traffic is persistent, and fairly variable.
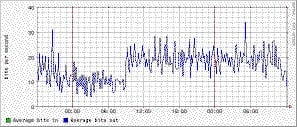 |
But a weekly sample shows that a poor silent, unattended node gets something of a break at the weekends. What's a gal to do? We see that traffic drops by half at weekends, from 20 bits per second to 10. This, as Robin suggests, gives credence to the theory that a lot of the Internet's static is generated by business computers, which are running Microsoft® Windows™., but which are left unattended when the corridor warriors depart their desks, and head downtown, to hunt for unprotected nodes.
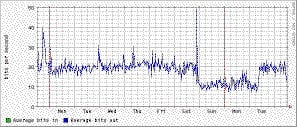 |
Now that's interesting. The monthly chart isn't too interesting, however, so we won't bother showing you it, but for the sake of completeness, here's a chart for the duration. It represents a routed but silent Internet node over the course of eight months silence.
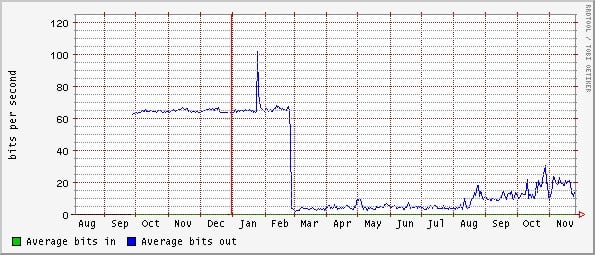 |
As we can see, it's going up.
Some of us have noticed that the noise quotient of the Internet has increased somewhat and, what with all the spam, the pop-up windows, the blog noise and Google being broken, things just aren't what they used to be. The 'be' being a thing that perhaps never was, or only ever existed as the romantic hope of someone's imagination. Our Robin brings us back to earth, and points to a few interesting implications of this data.
The hard figures we can draw are that modem users lose about 20 bits per second to Internet junk, which is just about tolerable. But owners of Class B networks, who expect to monitor 256^16 nodes, are probably more interested in the stats, as they pay for the data.
Techno-utopians have tried to school us that the "Internet" is frictionless and free. But now we look at the real Internet and, once we included background static in the picture, we can begin to discover where the real costs lie.
And the larger networks have a real cost here, as Internet static is multiplied exponentially. So what happens next?
From the technical follows the political: these guys may start to get selfish soon, and demand to be paid. For punters who've always accepted that "things" are "free", and never thought about the political economies of the Internet - this could be a real eye-opener.
The operators may well decide to throw the Internet's real freeloaders - geeks who contribute little real (in terms of technical or social) infrastructure, off of the payroll, at a macro-economic level. The political economies suggest that some day very soon Internet consultants may well be expendable to the people who really pay the bills. And if this cost is a form of pollution, which polluters must we bill? The guys whose computers are left unattended at weekends, leaking like an oil spill?
The Universe gives off a persistent background microwave radiation - and this provides astronomers with the historical data of how the cosmos was created. How much can you stand, and how much do you think the money men can stand before they pull on their radiation suits? And who do we send the bill to, at the end of the day? Let us know ®
