This article is more than 1 year old
Boffins buff bugging bugs
Roaches enlisted in War on Terror
As military scientists plan to dehumanise the battlefield, replacing humans with fighting robots, there's another trend bearing down on us from the opposite direction. Boffins are anthropomorphising select members of the animal kingdom to help in the War on Terror.
The latest species to receive its marching orders is the humble cockroach.
"You could attach a sensing device onto the back of a cockroach and send it into a place where you suspect they're making chemical weapons," Dan Brinker, a Sandia Labs scientist and professor at NMU, explains to the Scripps Howard News Service. And what do you know, he's done just that.
Tiny yeast cells which have been dyed to indicate the presence of a specific chemical are enclosed on the critters' backs, in an insulator called So Gell, and the insect army is then sent into battle.
"Cockroaches are robust," says Brinker "They can go into environments that humans can't withstand. If you can go in covertly, you can collect evidence without anyone getting spooked." Unless the enemy has trained its own killer roaches to seek and destroy the interlopers.
And what if the cockroaches decide to mutiny? That's a bug that could stop the bugs from completing a successful bugging mission. However, it appears that DARPA has already thought of that. Three years ago the military's R&D division held an "Insect Tracking Workshop".
At DARPA, this work falls under the scope of CBS (Controlled Biological Systems) research, and you can find much more about it here.
DARPA received $60 million to harness animal power in 2001, and the enthusiasm for animal metaphors are clearly infectious, as this slide from an unrelated project demonstrates:
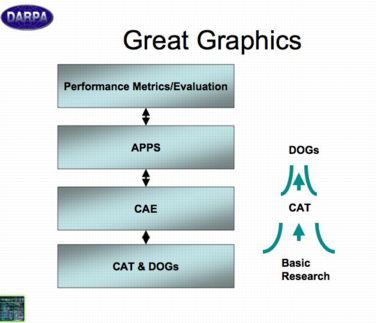 |
"The magic begins with us," promise DARPA's 'Imagineers', and they don't disappoint - although readers intrigued by research into 'Time Reversal Methods' maybe disappointed. Using Time Reversal, perhaps armies of cockroaches could be sent back in time to construct the missing WMDs which weren't there in the first place, retrieved, and then sent back to discover them, we mused. Alas the technology isn't quite there. Yet. ®
Related Link
Related Stories
Robogrunt: the US military's plans for robot armies
Invisible GIs to heal selves, leap tall building with nanotech
DARPA to invest in digital butlers
The self-healing, self-hopping landmine
