This article is more than 1 year old
Tom Clancy style look at war porn software
How many lines of code command US super gunship?
In the absence of solid news about what exactly is going on in Afghanistan as the US, and to a lesser degree us in the UK, bomb the hell out of the country, western newspapers have inevitably turned to features about the equipment we are using to bomb the hell out of the country.
But while a national newspaper editor may ask: what is the full rundown on the military equipment we are using?, we at The Reg are more interested in the more IT-related side. In this case: How many lines of code does it take to kill hundreds of Afghans?
The answer is 609,000 and this the number of lines of code in the software for the AC130U's computers and avionics systems. What's the AC130U? It's the huge gunship that has just hit the papers because it has been brought in for low-level precise devastation of various points so that special forces can be landed safely and then do whatever job they're there to do.
The AC130U is called Spooky and also called the "U-Boat" and is either the greatest example of heavy firepower in the world or hell in plane form depending on how you view war and whether it's on your side or not.
The 609,000 lines of code apparently make it the most complex aircraft weapon system in the world, although we're sure that Windows contains more lines. Amazing how small software can be when you put your mind to it (or care about how big it is).
Spooky contains one 25mm and one 40mm cannon, firing 1,800 and 200 rounds a minute respectively. It also has a howitzer-sized 105mm gun, firing six to 10 rounds a minute. That is a lot. All the guns poke out the left hand side and the plane circles over a target anti-clockwise.
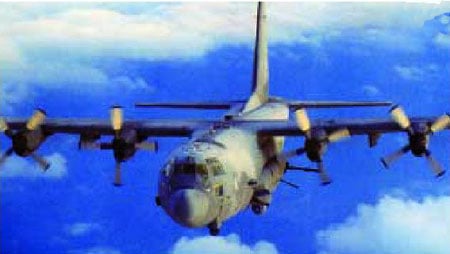
They are Hercules transports converted by special ops to be used for close air support, interdiction, armed reconnaissance escort and area defense missions. Here are two pics for you perusal. Neither very good but there you go.
If you want to know everything you could ever wish to know about it (and better pics) look here. ®

|