This article is more than 1 year old
Microsoft fails to renew its digital certificate
Hardly encourages e-commerce, does it?
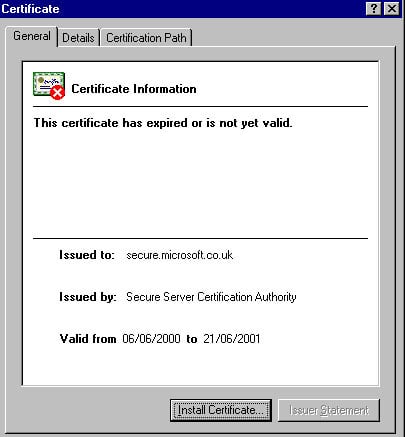 |
Microsoft has forgotten to renew the digital certificate on one of its ecommerce sites.
secure.microsoft.co.uk allows developers to purchase pre-release software, but its Verisign-supplied digital certificate expired last Friday (June 22).
A secure connection can still be established with the site but by confronting visitors a warning notice about the certificate Microsoft will do little to encourage ecommerce. Without the signed certificate its users can't be certain that the site really belongs to Microsoft at all.
In March Microsoft had to admit that Verisign issued two certificates in its name to a scam artist posing as a Microsoft employee. The certificates were of the sort used to digitally sign programs and the group who obtained the certificates might use them to trick users into running malicious code, signing Trojan horses and viruses with Microsoft's name.
To address the problem, Microsoft announced plans to develop software that would make sure the bogus certificates are recognised as invalid.
After that experienced you'd think Microsoft had learned its lesson about managing digital certificates. Apparently not.
Microsoft isn't alone in having trouble keeping to date with the administration of its secure sites. Last month security specialist Symantec also forgot to renew the digital certificate on a site designed to act as a showcase for its products.
F-Secure, another security firm, also got its digital credentials in a twist shortly after because a digital certificate issued to validate one site was applied to verify another. Its possible to have group certificates that verify a family of sites but in the case of F-In-Secure didn't set up this properly.
Thanks to Davoud Davies for telling us about Microsoft certificate expiry. ®
External Links
Microsoft's expired certificate
Microsoft Internet Explorer server certificate validation vulnerability (the perils of crackers impersonating trusted sites)
Related Stories
Microsoft vexed by falsified certs
UK govt new encryption system only works with MS kit
F-In-Secure muddles up its digital certificate
Symantec forgets to renew its digital certificate
